Essential Cybersecurity Strategies for Industry 4.0 Protection
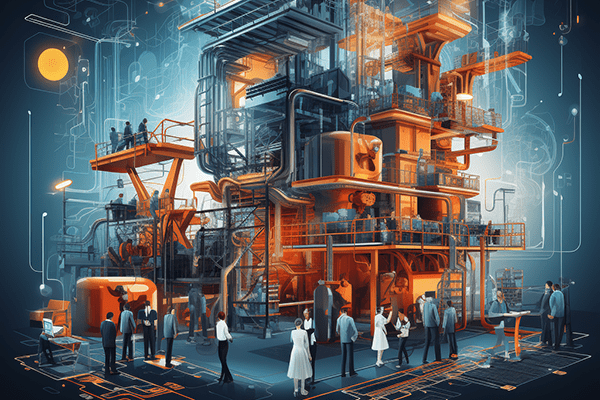
Industry 4.0 has ushered in a new era of technological innovation, transforming the way industries operate and creating unprecedented opportunities …
Essential Cybersecurity Strategies for Industry 4.0 Protection Read More »